Hello World!
I wanted to take a look at a recent phishing campaign that was uncovered after being active for roughly two years, interesting for me as I have studied Aviation operations in the past and have good knowledge of their procedures and practices.
So let’s see what we know about this threat actor… They are suspected to be operating out of Nigeria, and from what we can gather aren’t very technically skilled. A quote from the Microsoft Security Intelligence team who first released research of these attacks in May 2021 and talks of a “dynamic campaign targeting the aerospace and travel sectors with spear-phishing emails that distribute an actively developed loader, which then delivers RevengeRAT or AsyncRAT.”
Okay! So what’s a RAT? A RAT or Remote Access Trojan is another form of computer malware, a cousin of the computer virus and brother of the rootkit. This program acts as a backdoor to the victims device, it will then establish communications with a command-and-control server, where it will receive further instructions from the attackers. This communication could be to upload further malware such as a rootkit or crypto locker and/or exfiltrate data and information from the victim and hold it for ransom (However a sophisticated attacker might first look for privilege escalation and then pivot to a machine that hosts something like… Hmm anything really, a database for example. Or if your team is having a really bad day, they might even get into your backups if you haven’t taken the necessary steps to store these backups off-site and on tape, as well as following your organisations guidelines… and put simply, you cant restore if the backups f****ed)
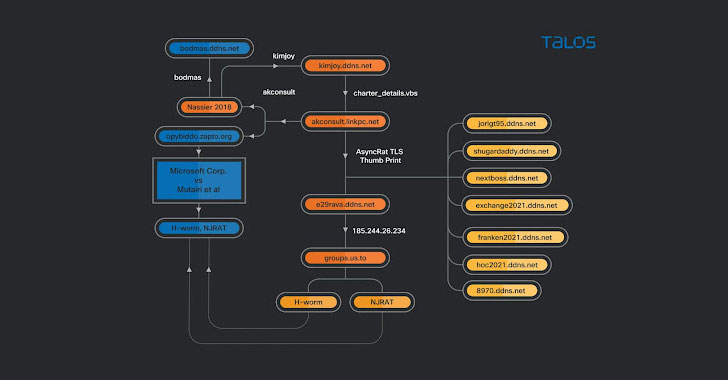
To read from the Cisco TALOS post here: researchers Tiago Pereira and Vitor Ventura said. “The actor also buys the crypters that allow the usage of such malware without being detected, throughout the years it has used several different cryptors, mostly bought on online forums.” Now this is a tactic that’s become more prevalent the last few years with less skilled threat actors, who often lack the programming knowledge to create malware or even edit malware in some cases. This use of a different crypter, format or language will change the outcome of the file (In some cases actors have just taken malware and switched it to another language, compiled it and boom). This isn’t a magical bypass by any means, but our signature-based security devices will fail to recognize this threat and take action, for this we need a solution for the canonicalization of this data; but, ultimately lack this ability.
Our Signature based security devices will look for known signatures given off by documented malware, this could be anything from know IP addresses of command-and-control servers, known malicious domain names to a SHA256 hash of a known malicious file. It’s in the latter where one single character will change the hash completely and render this form of security ineffective until it is given the new intelligence. However this is where other forms of security device would pick up and identify the threat, a reminder to layer your security… but not to over-complicate things.
So, we’ve covered the geeky stuff about what’s going on here. Now for the heart of this campaign which is less geeky and probably a familiar sight to any security staff… The vector of attack? Social Engineering.
In this case it was a spear-phishing campaign, the emails aren’t anything fancy just very legitimate looking as you would expect from pretty much any spear-phishing campaign as they tend to be the hardest to spot, it was through these phishing emails that the victim would be prompted to install (a disguised version) of the remote access trojan as shown by the email at the beginning of my post.
Source: https://thehackernews.com/2021/09/malware-attack-on-aviation-sector.html

You must be logged in to post a comment.