[Update 11th May 2022: I am going to be making changes soon to improve readability of this post, I understand it’s a little more complex than what I am aiming for.]
Passwords: So, let’s start off with the most important question, what makes a good password?
- Passwords should be at least 14 characters in length.
- Passwords should be unique, a different password for every account.
- Passwords shouldn’t contain personal information, such as your birth year or even things like your old street name.
- Passwords should be a mixture of characters; letters, numbers and symbols, as well as case differences.
- Passwords should be kept secret, even from those you love and trust… You don’t know how seriously they take security.
Now I wanted to look at the UK NCSC’s guide and their three random word guidance. They recommend using, well… Three random words, claiming that this is more secure than “complex passwords, which can be difficult to remember and yet guessable for criminals.” (www.ncsc.gov.uk, n.d.)
NCSC Technical Director Dr Ian Levy said: “Traditional password advice telling us to remember multiple complex passwords is simply daft.” (www.ncsc.gov.uk, n.d.)
I’m going to be upfront; I disagree… Let me tell you why.
Since about 2014 I have been using a program called KeePass, this program has withstood external penetration tests I have been aware of. With the testers being unable to breach the software. This was my father’s implementation to his organization; it wasn’t adopted by all users. However, the admins had been using it, successfully keeping attackers away from important passwords.
Before I show you KeePass, I will look at the positives of the NCSCs method. The first one that springs to mind is simplicity, not every user is exactly confident installing software on their computer and coming up with three random words is certainly much simpler and easier to understand than a long list of password requirements. Secondly, compared to a password manager there is no risk of “losing” many passwords in one go. Things could sometimes break, or you may lose access to the media device that held your password database or key file, this isn’t a problem with using the 3RW method. Finally, password managers can be quite tedious… Sometimes you may find yourself frustrated and having to go in and out of a password manager multiple times across a short time span. Not just that but the act of having your database on X media and key file on Y media is intimidating to some.
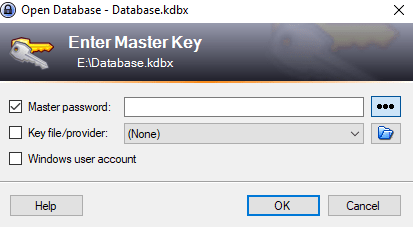
Here’s the KeePass prompt you see when you have created a database, which is a simple process that you will be taken through for the first time. When you do create your database, you’ll be given the option to create a key file or link your database to your windows user account. (I believe this must be a local account, so you may need to switch account type on Windows.) I strongly suggest using one of these, this is your multi-factor authentication aspect of KeePass.
- Something you know, your password.
- Something you have, key file or windows user account.
We will go over MFA next and explain this in a little more detail, but for now my recommendation for a basic setup of KeePass is to just keep your database on a USB (You will need the “portable” version for this.) and the key file on your personal computer. Best practice would involve making a backup/copy of both the database and key file, this isn’t required but recommended. A common issue with this is that you’ll constantly be adding new entries to your manager, so will need to make sure you update both databases. Always save your main database, but periodically make saves to your backup maybe once a fortnight.
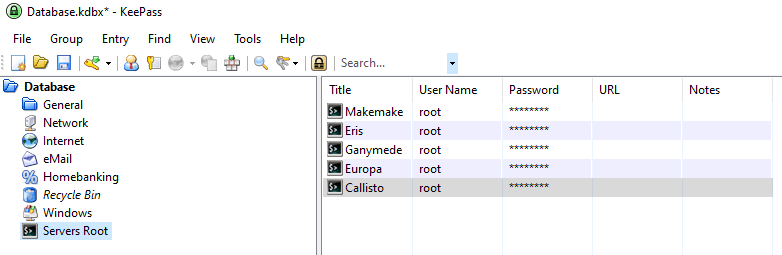
Here’s a KeePass database, fun fact about me: I like to name my servers after planets and workstations after satellites. (Mainly moons but inclusive of other satellites.)
We will go over creating entries and password generation in a moment, but let’s say I wanted to now log into the root account on Ganymede. For the sake of my point. I’m going to ignore potential issues with copying passwords onto VMs, a note for the geeks is to configure SSH (or RDP for windows machines) and port forwarding so you can access machines from a terminal line or software like PuTTY. I would simply right click on my Ganymede entry, click copy password and my password will be copied to my clipboard for 15 seconds to paste into my terminal line. You would likely use it for something like your Amazon account or PayPal account. The same applies for your username, the URL field is for putting the address to the website (or IP to server) and notes for… well, notes.
So how do we use KeePass to create passwords? Start by right clicking anywhere in the folder you wish to create an “entry”, then simply click add entry.

You’ll see the window on the left, click the little key next to the password box and you will be presented with a drop-down selection, click on open password generator and you will get the second window on the right pop up. This is your password generator; it lets you determine how you want your passwords to be created. This is a good place to apply those password rules, plus this will keep them all together and mean you no longer need to remember any password other than your database master key. However, do make sure you save after any edits and don’t lock yourself out of your accounts. Here would be a good place to implement a random word password, but opting for five words over three as the reward for getting into a password database is worth much more of a wait to an attacker.
Lastly here before we move towards our conclusions, let’s look at how many combinations there are if we take the 171,476 words in the dictionary and have users choose 3.

This gives us an output of 8.403325462709 × 1014 (840 trillion) possibilities, now I’m going to save us both the maths on this next one but let’s add numbers to letters and you have a different story, the number increases even more, then even more when you start randomising where capital letters may be… I’m going to say that a little bit of open-source intelligence is likely to eventually narrow down a person’s three-word password, if we’re talking about how many words the average person has in their vocabulary the estimations work out to about 20,000, that’s a significant drop from our original pool of over 170,000. We are human, one of our inherent weaknesses is sticking to what we know… Users are still going to be using words that mean things to them or set passwords like MarchTwentyTwo. Without adequately addressing these psychological factors of security, the three-word method will suffer from similar issues as we have had in the past.
In conclusion I have demonstrated a free open-source password manager that I believe is simple, whilst not as simple as the NCSCs method and many more steps to go through, I believe the use case for password managers is not going to disappear. With so many accounts nowadays, users will struggle to remember their unique passwords to every online store or their social media. Whilst the NCSC themselves are self-aware of this weakness, this means that a way to securely store their passwords is going to be required no matter what scheme you use to create them. This method will also come along with the same human level vulnerabilities that only true randomization can mitigate. Why think of a password when the application you use to store them can think of one for you?
I have decided to push these out piece by piece, this was a chunky read and if you did read it all then I am honestly thankful… You are taking steps to a safer online presence. I will demonstrate some little offensive techniques soon which will be linked into this post to give readers a much more informative experience. Additionally, as we just lightly touched on in this post there is something called Open-Source Intelligence (OSINT). We certainly will investigate when we take a look at phishing, but I encourage you to just give it a google, it’s likely something you do all the time yourself.
Come back next time where we will delve into multi-factor authentication, what is 2FA, 3FA? How effective is MFA? How can I use MFA to protect my account?
Thank you for reading, Sec rity really isn’t possible without u, Stay safe!
http://www.ncsc.gov.uk. (n.d.). NCSC lifts lid on three random words password logic. [online] Available at: https://www.ncsc.gov.uk/news/ncsc-lifts-lid-on-three-random-words-password-logic.

You must be logged in to post a comment.